Incognito can enable privacy for any cryptocurrency by connecting to external blockchains using inter-blockchain bridges.
The end goal is for fully decentralized trustless bridges, like Portal, to connect every blockchain with Incognito seamlessly. But as fast as we move, this takes time.
In the meantime, trusted bridges are being built to offer privacy to blockchains. They‘re called “trusted” because they innately require some level of trust in the bridge operators, since they aren’t fully decentralized. While we’re working on decentralization, this is mitigated by the fact that anyone can build a trusted bridge.
Developer resource: How to build a coin<>pCoin swap using Golang SDK
What they do
Trusted bridges are centralized or semi-decentralized ways of transferring cryptoassets between an external blockchain, such as Litecoin, and Incognito. It’s how you’re able to use coins like pLTC anonymously on the Incognito network.
When you shield or unshield your crypto, the bridge manages the custody and exchange of regular coins and their corresponding privacy coins.
How they work
When a trusted bridge is created for a blockchain, a privacy version of that chain’s cryptocurrency is first minted on Incognito.
Then, a custodial multi-sig wallet is created to hold the newly-minted privacy coins and any shielded crypto that comes in. These wallets must be equipped with functions that can prove that the coins are backed 1:1, and issue proofs when they receive/release coins.
The bridge then facilitates the exchange between privacy coins and regular coins.
Let’s take a step-by-step look at shielding and unshielding with trusted bridges. For this example, we’ll use Litecoin (LTC):
Shielding
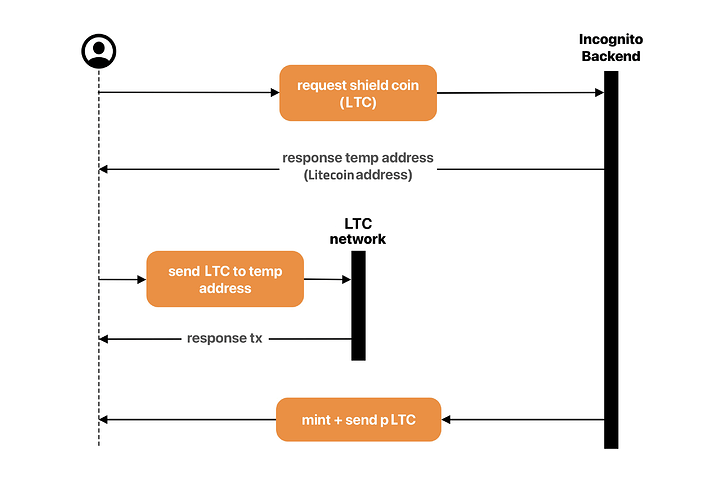
1. You request to shield LTC
In the “Assets” tab of the Incognito app, you tap “Shield my crypto”.
2. You receive a one-time address
The Incognito backend generates a one-time address (OTA) for you to send your LTC to.
3. You send 1 LTC to the OTA
From your non-Incognito wallet, you send 1 LTC to the one-time address provided.
4. Your 1 LTC is forwarded to the custodial wallet
The one-time address is not the final address, but a proxy. It forwards the 1 LTC to the custodial wallet.
5. Custodian sends proof of receipt to Incognito backend
The custodian confirms your coins have been received to allow the next step to take place.
6. Incognito backend mints 1 pLTC and sends it to you
Once proof of receipt is confirmed, privacy coins are minted at a 1:1 rate of your deposit and sent to you.
7. You receive 1 pLTC, ready to be used anonymously on Incognito
Shielding command flow:

Unshielding
Unshielding is the act of sending your crypto out of the Incognito network. It is similar to the shielding process, but in reverse.
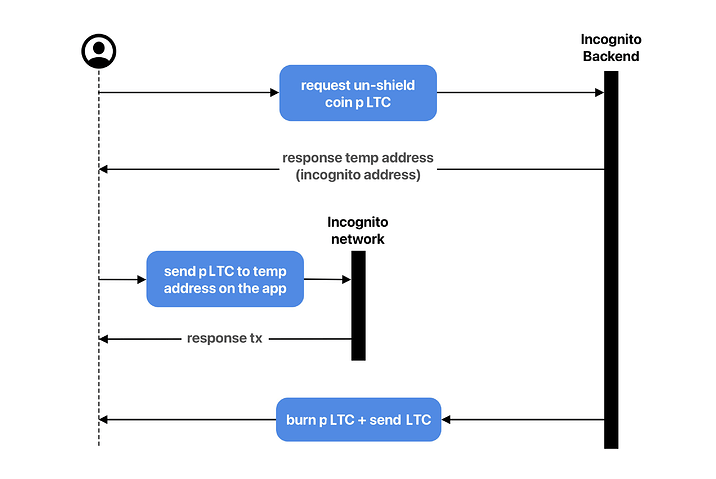
1. You initiate a transfer of 1 pLTC to a non-Incognito address
Once you hit send, the following steps take place on the network, invisible to you:
2. Your 1 pLTC is sent to a temporary address
Burning crypto (which will take place next) is a public transaction, so the temporary address is used to break the link. As the sender, you remain anonymous.
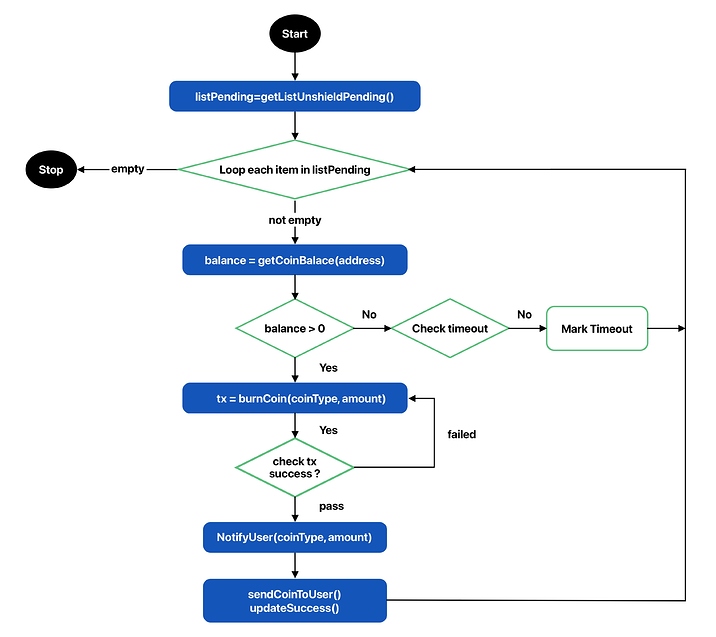
3. The Incognito backend checks the balance of the temporary address
This is to ensure your 1 pLTC is ready to be burned and no longer in your wallet.
4. The 1 pLTC is burned
Since privacy coins are meant to be used on Incognito, they can’t leave the network.
5. The custodian releases 1 LTC to the address you provided
Once the pLTC has been burned, the custodian can release an equal amount of LTC to your intended address.
6. The address you provided receives the 1 LTC
Now that the coins have left Incognito, they are no longer private. You can expect to transact them on external blockchains with their standard level of publicity.
Unshielding command flow:
Trusted bridges make adding privacy easy
Trusted bridges offer the same privacy as trustless bridges. Once your funds are incognito, they’re good to go.
Trusted bridges make adding privacy to any blockchain easy, and they’re much faster to create than trustless bridges. They’re the perfect way to spread privacy to the entire cryptosphere as we continue decentralizing the Incognito network.
For more on decentralization, explore Incognito’s pragmatic approach to decentralization.
If you have any thoughts or questions, don’t hesitate to share them with us in reply to this topic!