Introduction
Several cryptocurrencies use mechanisms by which coins are destroyed or “burned”, to reduce the total supply or create a burn proof. That means eliminating them by sending them to an ‘eater address’, which is not accessible by anyone since no one knows the private key to that address.
Burning coins is not an uncommon practice, as seen in Kyber Network’s KNC and Binance’s BNB. The typical reason for burning is that a reduction in total supply should lead to a higher coin price.
Another reason for coin burning is to achieve consensus. A burn proof is used as evidence in a distributed network, the actions of which will depend on this evidence. For example, minting another coin, or returning that coin after.
In Incognito, we use the burning mechanism to achieve consensus in mining, pDEX, and trustless bridges.
How to generate Burn Address
The formula to generate burn address is as follows:
Hash(G, “burnningaddress”, index)
where
-
hashis Keccak256 hash function -
Gis the base point of Edwards25519 -
“burningaddress”is a string to make sure the output of the hash function is unique -
indexis the minimum positive integer number such that the last byte of output is zero. It will make sure that the burn address belongs to Shard 0.
As a result, we use the burn address
12RxahVABnAVCGP3LGwCn8jkQxgw7z1x14wztHzn455TTVpi1wBq9YGwkRMQg3J4e657AbAnCvYCJSdA9czBUNuCKwGSRQt55Xwz8WA
generated at index = 68. Check the source code here for details.
Incognito’s burning and minting mechanism
Mining
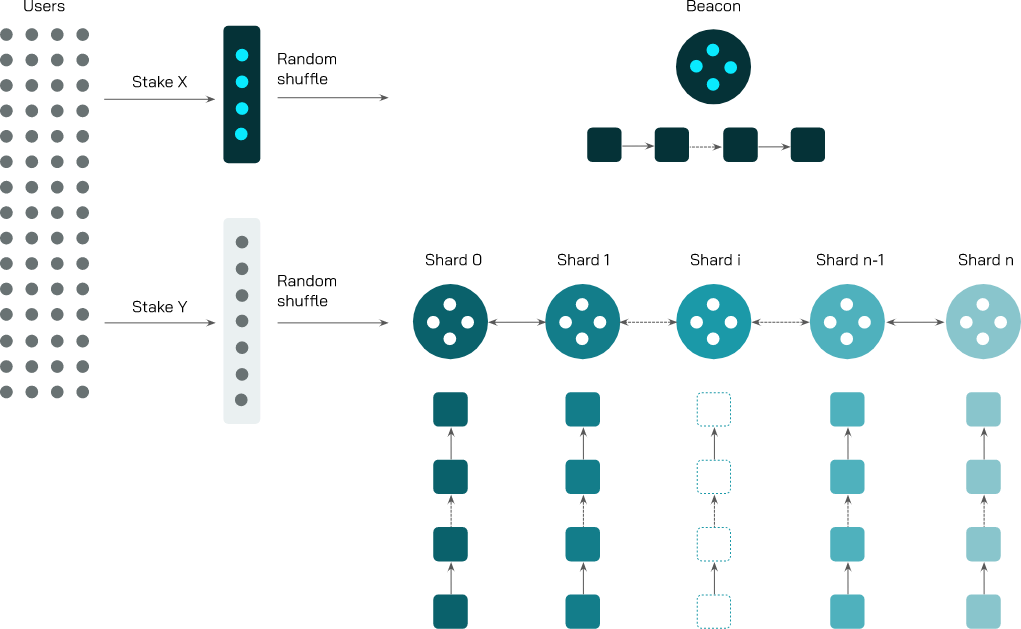
Figure 1: Staking process in Incognito
A user who has 1750 PRV is able to stake to become a validator. In a staking transaction, 1750 PRV is sent to the burn address. Later, if the user wants to unstake, the burn proof is used as evidence to return PRV to the user. A transaction minting 1750 PRV will be sent to the user’s address.
This 1750 PRV is unusable from the burn address as no one knows the private key of this address. 1750 PRV is minted. That means the total circulation of Incognito does not change.
Trustless bridge
Another case of mint and burn mechanism in Incognito is in shielding and unshielding transactions in the case of trustless bridges.

Figure 2: Process of porting public tokens into pTokens with Incognito vault
A shielding transaction is when a token from external networks (e.g., bitcoin, ethereum, binance, etc) is shielded via Incognito. For example, shielding 5 ETH from Ethereum means 5 ETH will be locked and 5 pETH will be minted on Incognito. The user needs to provide proof to Incognito to show that their ETH is locked. Then, a transaction minting 5 pETH will be sent to the address of the user.
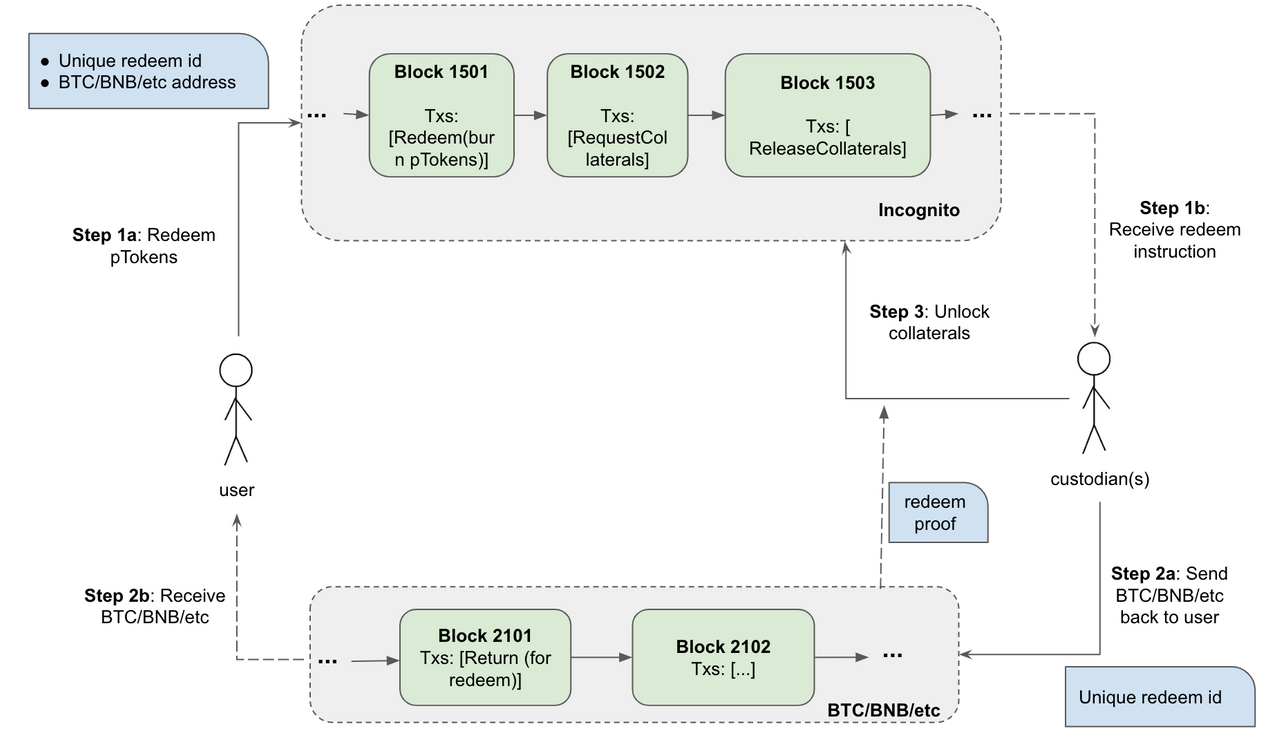
Figure 3: Process of redeem pToken with Incognito vault
As in the example above, to then unshield this 5 pETH from Incognito to Ethereum, the user first creates a transaction to send 5 pETH to the burn address. Then, the proof is verified to unlock 5 ETH and release it to the Ethereum chain.
At the end of the shielding and unshielding flow, the circulation on both chains remain unchanged.
pDex
Incognito is the first confidential DEX, based on the UniSwap protocol.
While most exchanges maintain an order book and facilitate matches between buyers and sellers, pDex holds liquidity pools of PRV and various privacy tokens. Trades are executed directly against these pools. The exchange rate between two tokens in a pair is set automatically using the ratio of the tokens in the pool.
Liquidity pools are maintained by a network of liquidity providers who add tokens into pDEX, in return for a proportional share of transaction fees and liquidity rewards.
Let’s say a user wants to trade token A for token B. The flow is as follows:
- First, the user creates a trade transaction in which token A will be sent to the burn address.
- Then, when the transaction complete, the corresponding number of token B will be minted and sent to the user’s address.
- Finally, the corresponding token A and token B will be respectively added and removed from the liquidity pool.
The final step makes sure that the total circulation of both token A and token B does not change.

